Merry Christmas。∠(*・m・)v Do you know about Christmas Scan?

table of contents
Hello.
This is Kawa from the Systems Solutions Department.
The end of the year is approaching so quickly.
It's already dark and cold outside by 5 pm, and at this time of year I just want to stay warm and cozy under the kotatsu and play my Switch all day.
December means Christmas!
It's been ages since Santa came to me, but
it's still nice to see the streets sparkling with Christmas lights, isn't it? ∠(*・m・)v
As the title suggests, there are Christmas-related things in IT as well, and
I'd like to ask if you're familiar with "Christmas (tree) scans"?
It's the name of a network attack, and techies have a lot of interesting neologisms
(although actually being attacked isn't really a laughing matter).
So, this time I'd like to write a little bit about Christmas scans.
What is Christmas Scan?
It goes by various names, such as Christmas scan or Christmas tree attack, but
this is all derived from the control flags in the packets.
Attackers
usually use stealth scanning as a method of port scanning to avoid being traced, and this is one such method.
Packets (in this case, TCP) contain a 6-bit section called control flags,
which are used to control connections. ACK and SYN are well-known examples.
The Christmas scan uses the following three of these flags:
URG (Urgent)- Contains data that needs to be processed urgently (with priority).
PSH (Push)- Passes data to the upstream server immediately without buffering.
RST (Reset)- Forcibly disconnects the connection.
Aside from RST, these flags might be unfamiliar to many.
Christmas scans are an attack technique that sets the bits of these three flags to "1" and
sends them as the first packet to gauge the target's response.
Why Christmas?
As mentioned above, this is due to the three flags being set, but that doesn't really make sense, does it?
Actually, you need to capture the packets and visualize them with Wireshark or something similar, but
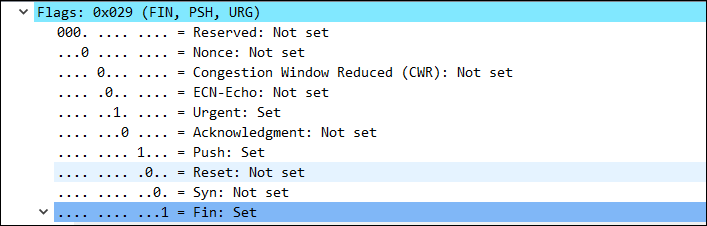
the flag section is colorful, isn't it? In addition, the flag structure is cone-shaped, like the right half of a tree, so
it looks like the tree is colored, which is apparently the reason.
⬇You

don't really see it like this.
Why is this an attack?
This is more of a port scan than an attack, so it's more accurately described as "preparation for an attack."
As you know, TCP packets follow a three-way handshake flow like SYN-ACK-FIN.
But what happens if an out-of-state packet arrives, ignoring this flow?
- If the port in question is open
, although the behavior may differ depending on the OS, it's not a SYN or anything
that the port is open
like that, so basically, if the port is open, it won't respond at all. The lack of response makes it easy for a third party to find out
- If the port in question is not open,
it is not permitted, so it will basically return an RST packet.
However, the sender will know that the port is "closed".
Incidentally, according to Windows specifications, it seems that it responds with an RST regardless of whether the port is open or closed, so
there is a possibility that the OS could be identified.
Also, the behavior of sending an RST or not varies depending on the firewall or UTM, so
depending on the combination with other attacks, there is a risk that open ports could be identified.
complete

 14
14







