Is your VPN connection really secure?

table of contents
Hi,
My work table at home is made from a box of Ehime mandarins 🍊
this is Kawai from the Systems Solutions Department.
The season is gradually turning towards winter.
I, too, tend to work remotely and stay indoors on cold or rainy days.
Although there is a trend towards returning to the office, I think there are still many companies that have introduced or are promoting remote work since the COVID-19 pandemic.
Along with this, the use of remote access VPNs from home has also increased, but is it really safe to operate them?
In this article, I would like to write about the mechanism and challenges of remote access VPNs
Advantages and Disadvantages of Remote Access VPN
First, let's organize the basic advantages and disadvantages of remote access VPNs
The main purpose of a remote access VPN islikely to be to securely connect to the company network from home or while traveling.
Next, when connecting to public Wi-Fi in cafes, etc., I think it's useful for ensuring security when connecting to insecure wireless standards such as WPA (althoughideally, you should just not connect in the first place...).
(Evil Twins attacksThere are also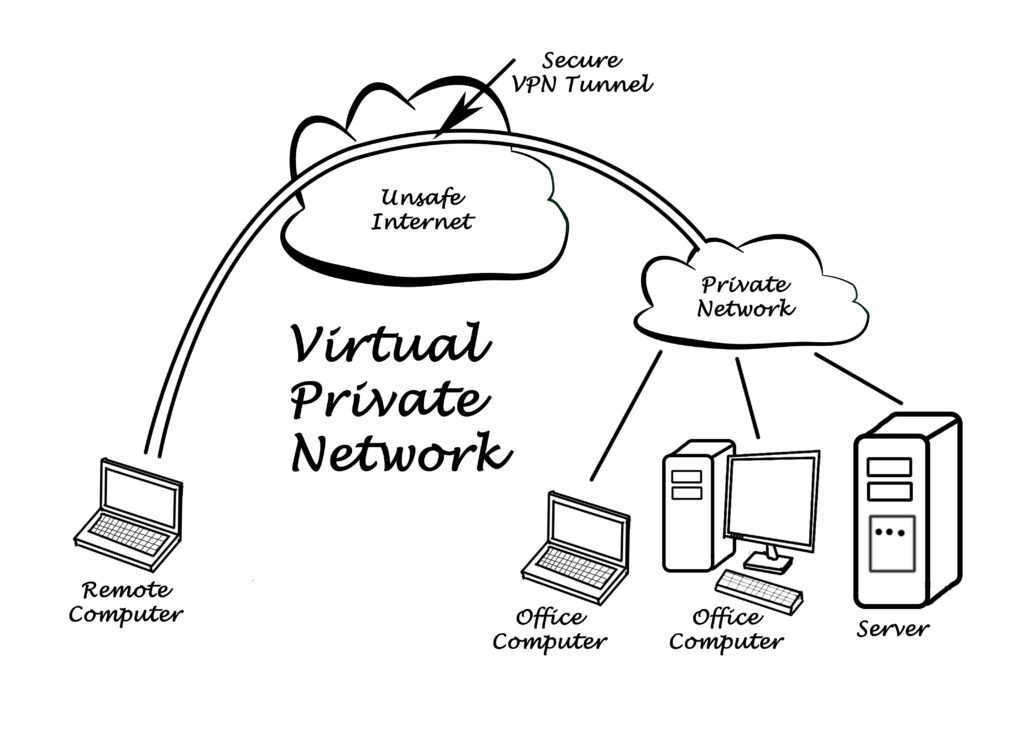 *For more information on the types of protocols used in wireless connections, please refer to the following Kaspersky article
*For more information on the types of protocols used in wireless connections, please refer to the following Kaspersky article
:https://www.kaspersky.co.jp/resource-center/definitions/wep-vs-wpa
■ Advantages
One of the main advantages is "encryptiondata
With a VPN, even when using a public network such as a cafe, communication up to the VPN server (such as a company router) is encrypted, thus reducing the risk of interception.
Furthermore, as mentioned earlier,secure access to local file servers and internal systems located within the office, meaning that necessary information for work can be obtained virtually from anywhere.
Additionally, routing settings enable connections from outside the office using the office IP address as the source (a so-called zero route), even in environments with IP restrictions. Very convenient.
■Disadvantages
However, one disadvantage to keep in mindthat even with a VPN connection, not everything becomes completely secure.
While this is the flip side of the benefits,VPN encryption only applies to the path from your home to your office.
Beyond that point, internet access is not secure even via VPN unless it's encrypted separately using HTTPS or similar protocols.
Furthermore, there are concerns regarding communication speed and connection stability.
Because VPN connections involve encryption and routing of communications, the connection may be less stable than usual.
The decryption and re-encryption of encrypted packets also increases the load on the router acting as the VPN server, and in some cases, this may affect the local internet connection.
How remote access VPNs work and what types are there?
There are several methods for remote access VPNs, each with its own advantages and disadvantages.
This paragraph briefly introduces some of the most commonly used methods.
(Each method name is a hyperlink to an article from "SE no Michishirube" (SE's Guide). Please refer to it for more detailed information.)

[IPsec/L2TP]
IPsec (Security Architecture for Internet Protocol or Internet Protocol Security) is a protocol that authenticates and encrypts data packets, and is used in combination with L2TP (Layer 2 Tunneling Protocol).
Authentication method: Pre-shared key or certificate.
Advantages: Provides high security and is supported by default in many operating systems.
Disadvantages: Encryption processing is limited to connections in NAT environments, which may make configuration difficult depending on the environment.
In terms of operation, it first encapsulates packets using L2TP and then tunnels the data link layer. Since
L2TP does not have encryption capabilities and is not secure enough on its own, the packets are protected with IPsec to ensure confidentiality and integrity, and encryption and authentication are provided using IP protocols such as AH and ESP.
[SSL VPN]
SSL VPN is a method of creating a VPN tunnel using HTTPS.
It can be used from a web browser and encrypts data using the SSL/TLS protocol.
Authentication methods: ID/password, one-time password, certificate, etc.
Advantages: Works with standard web browsers, making it easy to connect even in NAT environments.
Disadvantages: Depends on web traffic, so the number of compatible applications may be limited.
Generally, TCP/443 is available, making it simple. Furthermore, it requires less processing than IPsec/L2TP, resulting in more stable communication speeds.
Note that if there is a conflict with other services, the port number may need to be changed.
[IKEv2]
IKEv2, when combined with IPsec, provides a VPN that is particularly suitable for mobile environments.
Authentication methods: Certificate authentication, EAP (Expanded Authentication Protocol)
Advantages: Quick re-establishment of connection, robust connection even while on the move.
Disadvantages: Compared to other methods, it is not supported by many devices.
Is VPN really safe? - Considering the concept of defense in depth

That was a long introduction, but now we come to the main part
VPNs are one option for enhancing remote access security, but they certainly don't provide complete protection on their own.
To protect critical data and systems,a multi-layered, multi-level defense based on the zero-trust principleis necessary.
■ Newly Discovered Vulnerability (CVE-2024-3661)
Around May 2024, an attack method was reported that poisoned routing tables even under VPN connections, preventing communication from passing through tunnels.
Details:https://jvn.jp/ta/JVNTA94876636/
This method uses DHCP option 121, and although the attacker needs to have a malicious DHCP server within the network, it
has become a topic of discussion as an attack method that threatens intranetworks that were previously thought to be secure.
■Cases where actual VPN equipment became the entry point:
As a more recent example,the incident at Osaka Acute Care and General Medical Center in 2022.let me introduce
In this case, the hospital system shut down due to the attack, and all responses had to be done manually, taking about a year to fully recover.
According to the investigation report,https://www.gh.opho.jp/pdf/report_v01.pdf
The intrusion route in this case was a supply chain attack via E Company's catering center.
The firmware of firewall Z, which was the entry point for the intrusion, had not been updated, and the leakage of the device's ID and password was also confirmed
認された。また、病院は C 社の依頼にしたがって、ファイアウォール Y において、E 社の情報システム
enabled RDP communication (port number: 3389) from E Company's information system to be constantly connected via firewall Y, and subsequently failed to monitor or improve its operation, resulting in
め、E 社への攻撃が病院に波及した。
The above is a quote from "4.2.3. Summary of Technical Causes" in the report, but this case demonstrates that the head office is not the only entry point.
So-called supply chain attacks, where intrusions occur through VPN equipment at branch offices or affiliated companies and then spread to the head office via a closed network, occur frequently.
This highlightsextremely vulnerable once it is breachedthat no matter how secure the entry point is, an intranet network becomes
Therefore, even if communication is encrypted via a remote access VPN, if the connecting client is already infected, the VPN is meaningless.
■The Zero Trust Concept
Zero trusta concept based on the principle of "do not trust," where all communications, devices, and users accessing the network are verified and authenticated(a pessimistic view of human nature).
By combining VPN connections with access control, verification of communication content, and two-factor authentication, risks are minimized.
One concrete solution is to utilize authentication services such as Azure Active Directory (Azure AD).
Azure AD allows you to set authentication policies for each user's device/application, enabling granular control over access from outside the company.
For details:https://learn.microsoft.com/ja-jp/azure/security/fundamentals/zero-trust
■ In addition to endpoint defense and detection
, unfortunately, no matter how much protection is put into authentication and the pre-intrusion stages, it is impossible to completely prevent malware from infiltrating client-side PCs and other devices.
Therefore, in preparation for any potential intrusion or infection,collecting and monitoring logs using asset management software and implementing endpoint security productsare becoming almost essential.
*For an overview of endpoint security, please refer to our previous article ▼
・Easy-to-understand explanation of endpoint security
summary
While VPNs are certainly convenient and powerful, the idea that "I'm safe because I'm using a VPN" is dangerous.
With remote access VPNs, only the communication from your home to your company router is encrypted; the internet communication beyond that is not protected.
To ensure proper security, it is important to adopt a multi-layered defense approach, zero trust, and a flexible design that incorporates authentication infrastructure.
Incidentally, one notable development is that Microsoftstating that they will deprecate PPTP and L2TP in the futurepublished
*PPTP is inherently too vulnerable and should not be used.
In the future, there may be a shift towards SSTP, which is not covered in this article, and the aforementioned IKEv2.
https://techcommunity.microsoft.com/blog/windowsservernewsandbestpractices/pptp-and-l2tp-deprecation-a-new-era-of-secure-connectivity/4263956
https://ascii.jp/elem/000/004/227/4227428/#:~:text=%E3%83%9E%E3%82%A4%E3%82%AF%E3%83%AD%E3%82%BD%E3%83%95%E3%83%88%E3%81%AF%E3%80%812024%E5%B9%B410,%E3%82%92%E6%8E%A8%E5%A5%A8%E3%81%97%E3%81%A6%E3%81%84%E3%81%8F%E3%80%82
complete

 9
9







